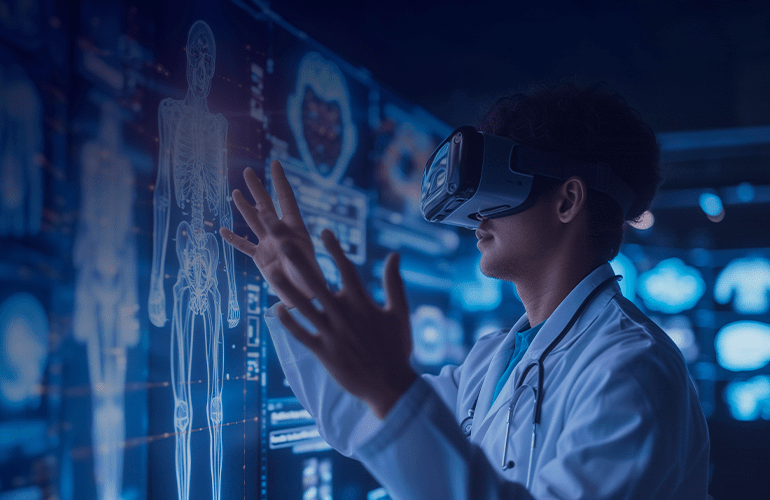
Building engaging and secure mobile applications
Do you feel comfortable with sharing your geo coordinates or payment details in your mobile app? Probably, not. Statistically, only 6% of respondents don’t hesitate while inputting their personal data into the application. Pavel Novik speaks on how testers and developers can help overcome the challenge and instill trust in users.
We live in the era of Big Data, where the Internet of Things and smartphones are ubiquitous. Each month we adopt new applications that require us to enter personal information, share our geo-coordinates, or ask to observe our browsing habits. Obviously, the main goal that marketers are pursuing is to collect social profile data and improve user acquisition.
The more personal data that marketers obtain, the better they can serve their users. However, users do not typically have much desire to help them.
Sharing is scaring?
According to the Global Consumer Trust Report 2016, the number of mobile users who feel comfortable with the idea of sharing information has decreased.
In 2013, 21 percent of the respondents said they would eagerly share with the application. By 2015, this number has fallen to 6 percent. The scope of “reluctant sharers” who share data only because they have no other choice if they want to use the app has leapt to 41 percent from 2014’s 33 percent.
This data should serve as a wake-up call to the mobile industry to collaborate and do more to instill consumer trust in mobile services. There are a number of practices on asking users for more information such as social sign-in options and bonuses in the exchange for extra data.
No matter which of them you adhere to, one thing remains constant: you need to be sound clear and reliable. Obviously, a good marketer should be aware of the security issues relevant to its app.
Users must feel confident installing the app and using it wherever they might want to. However, most public Wi-Fi networks lack security. So it would be a wise choice to disable automatic connectivity to such networks to prevent loss of important data.
Data leaks are the concern where users are expected to sync data to the cloud. The vendor’s protection mechanisms cannot be controlled even if the company’s security policies comply with best practices. To tackle this issue, it is recommended to ensure a different password for every app or service.
However, most of the security shortcomings are to be tested beforehand, on the development and testing stages of the security lifecycle…
Read the full article here.