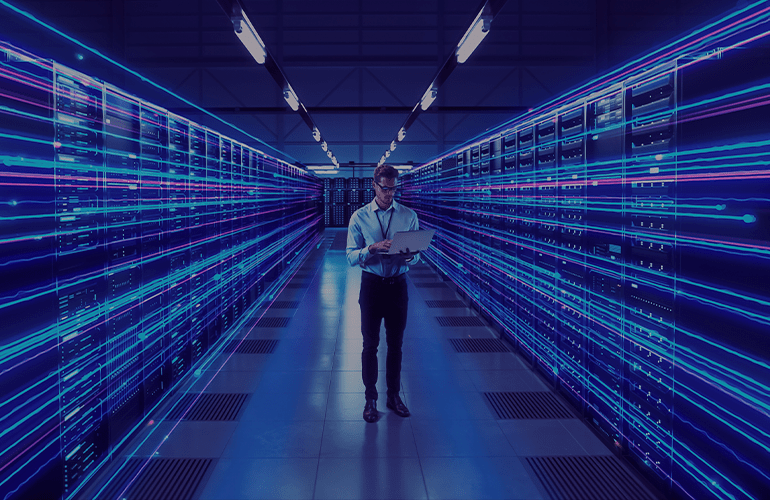
Gentleman`s kit of a security tester: are the development skills necessary?
What skills do you need to possess? Operating systems are everywhere today. Every day we send thousands of requests via laptops, smartphones and tablets, but do we remember our data security and confidentiality? The article by Anna Andreeva.
What should you know to test security?
In fact, the growth of web and mobile applications usage causes the leakage of users’ private information. Thus, security testing becomes an essential part of application development in general and web app testing in particular. But what an engineer needs to know to perform security testing?
First of all, you are to understand that security testing is not only about the application itself, but also about environment testing and check of information transfer and storage methods. The QA engineer should know lots of things apart the programming languages.
Of course, when a tester knows the application technology s/he understands where to search for bugs and how to fix them. For example, applications developed applying the ASP.Net by default use the built-in mechanisms of validation data, while the PHP programming language presupposes additional integrations of user entries.
When performing testing procedures keep in mind that application always runs in some operating system: a server, a laptop or a smartphone. Therefore security testing requires knowledge of system administration, and the skills of an experienced user. For example, if access to the server is provided with «low» rights, the engineer should know the way of escalation rights to the admin user. To do this you`ll need to understand how the register operates and how to launch services, processes and events logging systems.
Next thing in this list is knowledge of network technologies. Often hackers do need to attack the application to get the information because it is possible to “steal” it during the transfer process. To prevent it you are to know OSI model, package structure and the network routing process.
For firewall security testing also requires for special knowledge. What you should understand here is performing of checks from process incomplete, bypassing the “fire wall” through trusted processes and the ability tested products to block execution of unauthorized code in kernel mode.
SQL injection is one of the most critical OS`s vulnerabilities. It provides access to the information stored in the application data base. Thus the knowledge of SQL request language and its dialects is necessary for a full scale security testing. Remember a successful attack doesn`t end on simple select requests.
To check the protection against the cross-site scripting, hackers integrate harmful HTML/CSS/Javascript code in DOM-markup or in a request, which allows them to redirect user to the necessary resource and block application processes or “steal” the session variables. To run this check you need the knowledge HTML, CSS and Javascript.
Poor algorithms of data encryption can also become the reason of information leakage. To detect this vulnerability an engineer should know cryptography basics and what methods of data encryption protect information and algorithms are really poor for information security. For example, protocol SSL v2 is used to transfer data between a client and server and it is considered to be quite vulnerable. Specialists advise to exchange it for SSL v3/TLS v1 protocols.
On the whole, security testing demands for specialized knowledge. It is not obligatory to have extended programming skills, but you are to have basic understanding of different technologies, their pros & cons. If you need to bypass data validation, then you are to understand how programming languages “process” user entries. To integrate SQL-request, an engineer should understand how connecting line is formed and how information gets to database, what returns to users.
For security testing programming language is a tool for information processing. To detect a defect it is unnecessary to write encrypting algorithms or to obfuscate the code while the program running, but you are to know what is variable, array, class, structure and understand how the entities cooperate.
In the end, I want to say that programming languages are not the key of successful security checks. But the understanding of application basic operating principals, their influence upon the used technologies, operating system and configuration is a-must.