Protecting against DoS attacks
The article by Aleksey Abramovich was published in Pipeline Magazine.
According to the Ponemon Institute, on average, one denial-of-service (DoS) attack costs the owner of a website, including those associated with telecom organizations, more than 166 thousand dollars.
Every year, DoS attacks are becoming more expensive as site owners increasingly intensify protection against them. But who is implementing these DoS attacks and for what reason? And what is the best way to be prepared to protect your website?
The birth of DoS attacks
The first DoS attack was registered in September 1996. The attack was addressed to the site Panix.com – the first Internet provider in New York.
However, this first DoS attack was not as impressive as one carried out by a 15-year-old Canadian using the handle ”MafiaBoy,” who attacked a range of commercial sites in 2000. One by one, he caused the collapse of the largest American portals – eBay.com, Amazon.com and Yahoo.com – thus demonstrating the vulnerability of those websites at that time.
The next wave of popularity in DoS attacks occurred in 2010 when hackers began to break, one by one, the largest e-commerce systems: PayPal, Visa, and MasterCard. Every year DoS attacks continue to gain power. To provide an idea, in 2005, the “strength” of an average DoS attack was no more than 100 Gbit/sec; this year’s most powerful attack has already reached 400 Gbps per second.
Both attacking and defending sides spend billions of dollars on this ongoing “virtual war.” In order to understand how to defend against DoS attacks, you must first be aware of their nature.
DoS attacks: types and possible protection
We have established that a DoS attack is a malicious activity that blocks the site for the use of legitimate users. A subset of this is distributed denial of service (DdoS) attacks, which involve multiple computers under single management. DoS attacks usually addresses one of three resources, which we’ll cover below.
Channel attacks – a traffic emergency
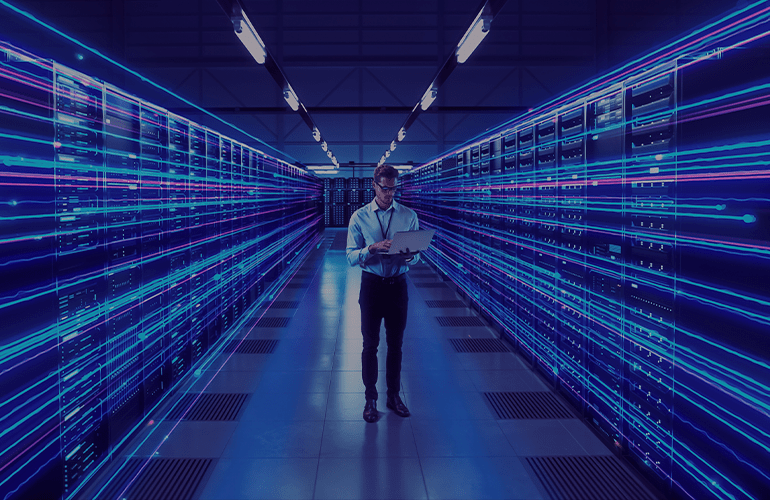
The most complicated and expensive DoS attacks for hackers and, thus, the most dangerous for the site owner, are attacks on the server network connection. Using a botnet or vulnerable servers, an attacker can generate a huge stream of malicious traffic to the website of the chosen victim.
Because of the large amount of “extra” load in the channel, legitimate users have problems while connecting, or can even be blocked. This situation can be compared to a traffic emergency where cars are stuck in a jam; the traffic is being caused by the DoS attack, and those “stuck in traffic” are the users trying to connect to the site.
The prevention of such attacks is quite expensive because of the need to purchase special equipment for detection and blocking. Otherwise, third parties, such as providers and data centers, should be engaged. The most effective solution is to create a “black hole” outside the server (onsite at the provider) to “catch” the traffic; imagine additional road lanes, which are consigned to offload the traffic jam. This is how black holes are activated at the start of a DoS attack. While all traffic is routed into the black hole, the owner of the website buys time to move the application to another IP address.
Attack on the CPU time – confused pupil
When attacking the CPU time, the maximum CPU load of the server becomes the target of such criminal attack. Imagine a student who is given 10 tasks to solve instead of one during a limited amount of time allocated for a lesson. Unable to concentrate on one, they eventually cannot do what is required.
The best way to defend against this type of attack is with a special software (for example, web application firewall of “WAF”), which is set on the server and filters out potentially dangerous requests.
Read the full article here.