Top 10 most common mobile app vulnerabilities 2016
In 2014 OWASP (Open Web Application Security Project) conducted a poll to gather mobile apps vulnerability statistics. The objective was to level up the mobile security and to allow individuals and companies worldwide to make informed decisions in the course of their mobile app development and security testing.
Survey results identified the top ten mobile vulnerabilities with the most frequent ones being weak server side controls, insecure data storage, and insufficient transport layer protection.
This year OWASP has updated the report. The surveyed audience has mainly included penetration testers (38%), security specialists (35.2%), security engineers and designers (27%).
The obtained results has revealed that during the last two years developers worked hard to secure coding and configuration practices used on server-side of the mobile application, establish mechanisms to protect data stored and ensure sufficient transport layer protection. Thus, the vulnerabilities 2014 have almost been combatted while the new bottlenecks have appeared.
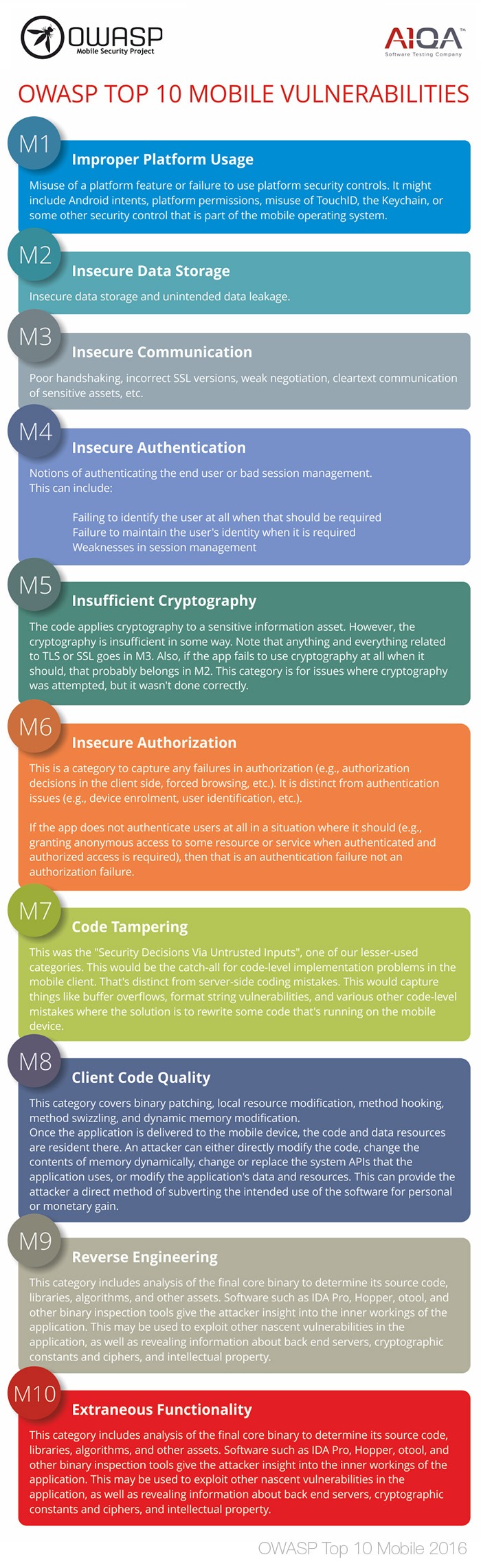
OWASP Top 10 mobile vulnerabilities 2016
- M1 Improper Platform Usage (new!)
- M2 Insecure Data Storage
- M3 Insecure Communication
- M4 Insecure Authentication
- M5 Insufficient Cryptography
- M6 Insecure Authorization
- M7 Client Code Quality (new!)
- M8 Code Tampering (new!)
- M9 Reverse Engineering (new!)
- M10 Extraneous Functionality (new!)
As for a1qa, keeping our customers’ information secure and private is a top priority for our QA experts. We greatly appreciate the OWASP survey results and consider them when testing and assessing security of our customers’ mobile products.